* What do Dr. Ivins’ lab assistants and colleagues say about the Apple laptop computer that turned up missing — which had been connected in the hot suite? Who used it and what was it used for in the privacy of the hot suite?
Posted by DXer on May 14, 2010
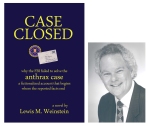
The FBI’s case against Dr. Ivins is clearly bogus: no evidence, no witnesses, an impossible timeline. The real question is why the FBI persists in sticking to such a pathetic story. What are they hiding? I offer one “fictional” scenario in my novel CASE CLOSED, judged by many readers, including a highly respected official in the U.S. Intelligence Community, as “quite plausible.”

DXer said
Ivins’ “missing” laptop is addressed in the memo by Richard Lambert that the FBI is withholding from the public.
The FBI has failed to produce any of the computer records from September-October 2001 sought by Kenneth Dillon.
The extent of the data google tracks is an amazing — it is an amazing goldmine for law enforcement.
http://www.dailymail.co.uk/sciencetech/article-5557619/IT-expert-reveals-extent-data-Google-you.html
Conversely, it would lead to a lot of exculpatory information if users and defense attorneys were able to understand and mine it.
In Amerithrax, there is no indication that the FBI even located the laptop that was in Ivins’ B-3 that was used by others.
Just think – the FBI could rely on this data tracking instead of anthrax-smelling bloodhounds.
They perhaps could have collected one less minnow trap from a Frederick, MD pond.
The District Court judge should be allowed to review Lambert’s memo in camera.
Anthrax, Al Qaeda and Ayman Zawahiri: The Infiltration of US Biodefense
http://www.amerithrax.wordpress.com
DXer said
Did Dr. Ivins view porn on this laptop that was installed in June 2001, was connected to the internet, and then went missing? Even some older men are obsessed and organize their daily life around viewing pictures of naked people, prisoners of animal hormones and programming. Was there really no way to determine what sites on the internet it visited?
From: Ivins, Bruce E Dr USAMRIID
Posted At: Friday, February 06, 2004 9:50 AM Posted To:
(b) (6)
(b) (6)
Conversation: Missing computer Subject: Missing computer
All: If you have an Apple Computer, MMCN D8694, please let me know. (It may be a
Powerbook laptop.) It is on my hand receipt, and I am unable to locate it. Information on it:
MMCN – D8964 Model Number – M5409 Serial Number – FC30317R465
Thanks.
Bruce Ivins USAMRIID
DXer said
The office in charge of tracking government inventory can use commercially available software that uses alternative methods for geolocation.
What does Pat Fellows think happened to the laptop? The GAO should publish her interview.
http://www.pcmag.com/article2/0,2817,2387748,00.asp
6 Ways to Find Your Stolen Laptop | PCMag.com
http://www.pcmag.com › Product Guides › Laptops & Notebooks
•
Jul 1, 2011 – If your laptop is ever lost or stolen, this security software will work hard to protect your precious data and help you recover the device.
DXer said
Dr. Randall Murchsays use of “match” in connection with Amerithrax was inapt. He discusses the importance of a snapshot in time.
Dr. Ivins had the largest repository of Ames anthrax. Why wasn’t his computer, including the Apple laptop, cloned in October 2001? A lesson learned is that if a particular agent is detected, then all laboratories being allowed and licensed to work with the pathogen clone the hard drives and turn them over to the FBI for examination. In Amerithrax, that might have been done in October 2001. As it was, Agent Van Harp didn’t meet with investigators for months (according to Ed Montooth).
The American Association for the Advancement of Science issued the following news release:
If the United States was the victim of a biological weapon, how would the government determine the source of the attack?
Not being able to answer that question is keeping leaders in the field of biosecurity up at night, experts said during a panel discussion at AAAS.
The response to a hypothetical bioterror attack would vary dramatically based on the source and motive for the attack. With such high stakes, the implications of misattribution could be extremely damaging to U.S. interests. “One of the grandest challenges of this world in biosecurity is discerning to a reasonable degree of certainty, if an event is it deliberate, accident, or natural,” said Chris Bidwell, a U.S. Navy commander currently assigned to the U.S. Defense Threat Reduction Agency and an adjunct professor of international relations at Georgetown University.
“I really do worry about developing and validating sufficient science so that when the call comes, that we have the tools in place,” said Randy Murch, associate director of research program development at Virginia Tech’s Research Center in Arlington, Virginia. “They have to be in place before the fact, and validated, so that when the call comes from the White House, U.S. government agency, or actually world leaders asking for U.S. assistance, that we can provide the kind of science which results in the information necessary to inform a proper decision.”
Bidwell and Murch, as well as Kristin Omberg, deputy division leader of the Decisions Application Division at Los Alamos National Laboratory (LANL), spoke 1 October at an event in the AAAS Auditorium. “Biosecurity: Confronting Existent and Emerging Unknowns” was the first discussion in the three-part “Science and Society: Global Challenges” series sponsored by the AAAS Office of Government Relations,http://www.aaas.org/gr/ the American Chemical Society,http://portal.acs.org/portal/acs/corg/content and Georgetown University’s Program on Science in the Public Interest.http://spi.georgetown.edu/ The discussion was moderated by NPR science correspondent David Kestenbaum.http://www.npr.org/people/2100747/david-kestenbaum
Murch said that the United States began to lay the foundation of capabilities for the forensic investigation of bioterror attacks in 1996, with the science and capabilities expanding rapidly following the anthrax attacks of 2001.http://www.fbi.gov/about-us/history/famous-cases/anthrax-amerithrax When members of the media and the U.S. Senate received letters contaminated with anthrax spores, the United States first started thinking seriously about the possibility of doing routine bio-detection in urban areas, Omberg said.
“In the run-up to the war with Iraq, there was a lot of concern because there was a legitimate question as to whether or not Iraq had chemical and biological weapons and would be willing to use them once we gave Saddam Hussein the ultimatum to leave the country,” she said. “And so that was when we started looking nationally at bio-detection.”
That interest in bio-detection led to the development of the BioWatch Program, a detection system by the Department of Homeland Security that monitors for potential airborne bioterror attacks. “If you think about what it takes to respond to an attack, it’s a tremendous drain on resources and it takes a lot of planning and a lot of preparation to be able to do that well,” explained Omberg, LANL project leader of BioWatch. “It [BioWatch] buys you time to prepare and figure out what you’re going to do.”
Lawmakers have expressed skepticism over BioWatch, specifically concerning false alarms caused by naturally occurring pathogens. Murch recalled learning of an alert triggered by BioWatch. “My first response was, what, dead rabbit near the sensor?” he said. “And it was a tularemia alert and it was a dead rabbit near the sensor.”
“Certainly early detection is important but you have to put things in context,” Murch said. “On the one hand, the technology is a very good technology and it’s tuned to alert on certain pathogens with certain sensitivity. But on the other hand, those can come from the environment. So then you have to investigate, you have to apply resources to determine where did it come from and how did it manifest before it can be determined whether what caused the alert was a natural or deliberate event.”
Omberg rejected the suggestion that BioWatch has produced false alarms. “It doesn’t tend to pick things up that aren’t there,” she said. “It’s just that it wasn’t due to a terrorist attack.”
However, the attribution of bioterror attacks remains extremely challenging because microbes mutate, Omberg said. “What we characterize today may not be what’s used and even what’s used might not be what we can characterize out of that three days later.”
“What we’re looking at is a snapshot in time,” Murch said. “It’s not so much though with some other kinds of forensic evidence.”
Meanwhile, before scientists can determine the source of the attack, the press is already covering it, Bidwell said. “You’ll be swimming upstream against a public opinion wave that is already starting to collect its own evidence and form opinions as to what happened. This, in turn, puts additional pressure on policymakers.”
Kestenbaum recalled while covering the anthrax attacks, reporters were told that anthrax samples had been identified that matched those found in the letters–but the use of the word “match” was later criticized for being imprecise.
Murch agreed that in that instance, “match” was inappropriate. There was a very close similarity between the samples and the FBI had gathered about as many specimens as were available at the time, he said, “but one of the great difficulties in this kind of forensic science is your base of known specimens is relatively limited.”
Moreover, Bidwell, a former trial lawyer, explained: “If you’re trying to use forensics to prove an attack came from outside the United States, you’re going to have a hard time explaining where the samples originated from, making them inadequate for attribution purposes.”
In a bioterror attack, scientists would need to arm the policymakers who would determine the U.S. response with an understanding of the complex science involved. “Just like with a jury, as evidence gets presented, you’re going to be explaining science to a policymaker who may not have a science degree,” Bidwell said. “The science actually doesn’t have to be as perfect as it has to be plausible and understandable.”
When it comes to BioWatch, “we have not had an attack so it has not done its benefit yet,” Kestenbaum said to Omberg. “Thankfully, you have never had a chance to shine.”
“God willing,” she replied, “we never will.”
Kat Zambon
DXer said
Frontline should submit a FOIA to DOJ for Dr. Ivins apple computer.
If they played hide-the-ball with his notebook showing the work with the rabbits, then they also may have played hide the ball with the laptop.
DXer said
If the laptop were there in 2001 and its hard drive cloned, there would be a wealth of information.
It’s call “imaging a hard drive”. My guess is that it would cost around $500 to $1,000 per hard drive. It requires removing a drive temporarily from a computer and using another computer to copy the entire contents to another drive. The process typically takes a few hours depending on the size of the drive. Once the imaging is done, the drive can be replaced in the computer.
To analyze the drive is more work. The image first has to be indexed and it can then be searched for the “good stuff”.
More here:
http://computer-forensics.sans.org/blog/2009/06/18/forensics-101-acquiring-an-image-with-ftk-imager/
DXer said
What lab notebook contains the record of the “old” formaldehyde experiments?
From: Ivins, Bruce E Dr USAMRIID
To:
Subject: “Old” formaldehyde experiments
Date: Wednesday, September 12, 2001 9:47:56 AM
Here is the information you requested on the Covance study:
Five years ago we made rPA vaccine/Alhydrogel with and without formaldehyde added. We tested
the vaccines after various periods of time of storage and noted (in guinea pigs) that the presence of
formaldehyde appeared to boost potency of the vaccine. It was unknown whether the boost in potency
was due to stabilization of the protein, or to an adjuvant effect. (Formaldehyde itself causes local
inflammation which would draw APCs and other cell types to the site.) The vaccine is now 5 years old
since it was formulated, and we wished to see (in the rabbit model) if there is any difference in potency
between the 2 vaccines. (The rabbit model is preferred over the guinea pig model in tests of anthrax
vaccine efficacy.)
Twenty-four New Zealand white rabbits (12 of each gender) were immunized with 0.5-ml
intramuscular doses of vaccine containing 50 micrograms rPA, Alhydrogel (0.5 mg aluminum) and PBS
(with formaldehyde, 0.02%).
Twenty-four New Zealand white rabbits (12 of each gender) were immunized with 0.5-ml
intramuscular doses of vaccine containing 50 micrograms rPA, Alhydrogel (0.5 mg aluminum) and PBS
(without formaldehyde).
Four rabbits (2 of each gender) will be controls receiving Alhydrogel and PBS.
Rabbits will be bled at weeks 2 and 4 for anti-PA antibody titers. They will be challenged
subcutaneously with virulent anthrax spores 6 weeks after immunization and monitored for survival.
This experiment will demonstrate whether the presence of formaldehyde in an rPA/Alhydrogel
vaccine increases or preserves potency.
– Bruce
DXer said
The Apple computer was hooked up to the internet, is that correct? Do server records show when it was last used to access the internet?
Based on the headers of emails sent from the Apple computer, isn’t the exact date that it was no longer used ascertainable?
DXer said
3/25/2004 302 Interview statement
—
Dr. Ivins did not have his emails from 2001 so as to be able recreate events.
“IVINS consulted with _____________ at USAMRIID Computer Services and learned that electronic mail (email) can be retrieved for a two year period, however it is expensive to do so. If more than two years have passed, it is not possible to retrieve email.”
Question:
Why couldn’t USAMRIID and FBI from the USAMRIID server identify email sent to and from the missing Apple computer by its IP and retrieve it?